Malware Masquerades As A Secure Banking Message
By: Jim Stickley and Tina Davis
November 7, 2017
After a big cyberattack, such as the data breach that hit Equifax recently, criminals frequently attempt to take advantage of the fear factor and trust customers and members have with their financial institutions. In a recent phishing campaign, discovered by Barracuda Networks, messages masquerade as legitimate and secured messages from banking institutions such as TD Commercial and Bank of America to trick people into installing malware onto their computers and devices.
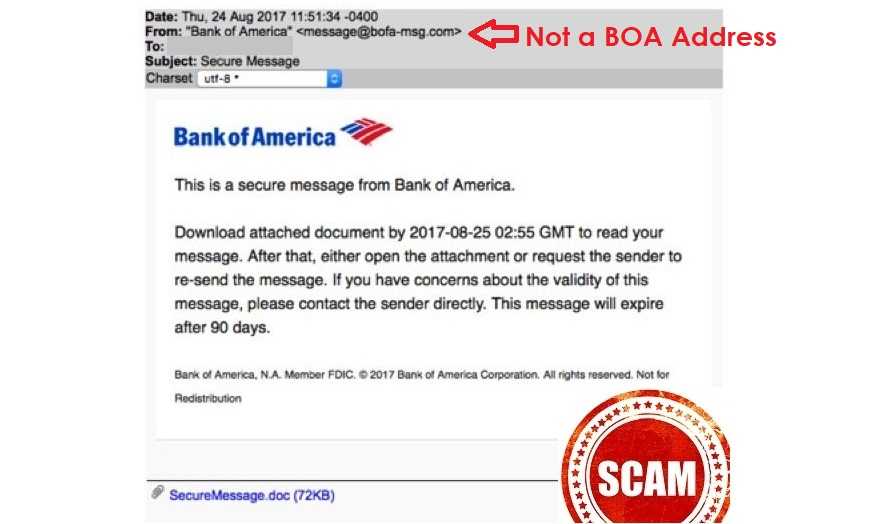
In this one, an email is received that claims to be a secure message from a financial institution. Inside is one of three possible phishing lures that researchers have seen thus far:
- An attachment with included malware
- Instructions to reply to sender
- A set of instructions to perform actions that executes the malware
They are pretty difficult to detect as fake because they use domain names that look very close to the real ones. For example, they may be “Bank0fAmerica” where the “O” is replaced with a zero. This is called do-jacking or typosquatting.
They also use actual logos and copy the confidentiality statements word for word, making it even more difficult to identify it as phishing. As a rule, simply never click on an unexpected link; especially if it is from an unknown email address.
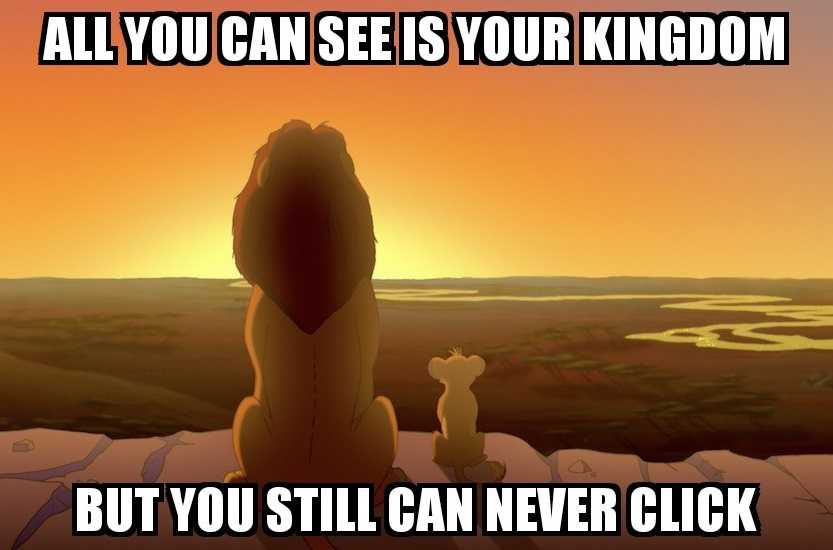 When receiving messages from financial institutions or any organization that has a confidential relationship with you, go directly into your account to check the secure message center rather than clicking links or attachments. There is no need to click links because these organizations always place those messages in your secure inbox in your account.
When receiving messages from financial institutions or any organization that has a confidential relationship with you, go directly into your account to check the secure message center rather than clicking links or attachments. There is no need to click links because these organizations always place those messages in your secure inbox in your account.
There are multiple variations of this attack and they make it past antivirus products in some cases. Once malware is on the device, it can be made more dangerous. The attackers may be able to remotely access it and turn it into ransomware, spyware, or information stealing malware.