 A recently discovered Trojan targets the Android operating system and has a big payload if it’s installed. Researchers at ESET confirmed that it doesn’t discriminate on the version of Android on your device and refers to it as Android/TrojanDownloader.Agent.JI. This one uses a fake Adobe Flash Player update to trick users. It is designed to monitor the activity of the user on the infected device and steal data, mimic the actions of the users, and ultimately generate funds from the click-through adware products. Although the ESET researchers didn’t come across instances of this, it is developed in such a way that it can also install ransomware.
A recently discovered Trojan targets the Android operating system and has a big payload if it’s installed. Researchers at ESET confirmed that it doesn’t discriminate on the version of Android on your device and refers to it as Android/TrojanDownloader.Agent.JI. This one uses a fake Adobe Flash Player update to trick users. It is designed to monitor the activity of the user on the infected device and steal data, mimic the actions of the users, and ultimately generate funds from the click-through adware products. Although the ESET researchers didn’t come across instances of this, it is developed in such a way that it can also install ransomware.
If you don’t regularly back up your devices, you should take that task seriously. The small amount of time it usually takes to do that can save a lot of time and stress later, should something like this strike. And if you haven’t installed anti-malware and antivirus products on all of your devices, that task should bump to the top of your priority list too. Keep those updated. Usually there is an “auto-update” feature and if you don’t remember to do it often otherwise, take advantage of that time and potential headache saver.
How the Malware Works:
This Trojan takes several steps to do its damage and they pretty much follow the below process. So, if you have gone through these steps, there is a good chance you have downloaded this malware.
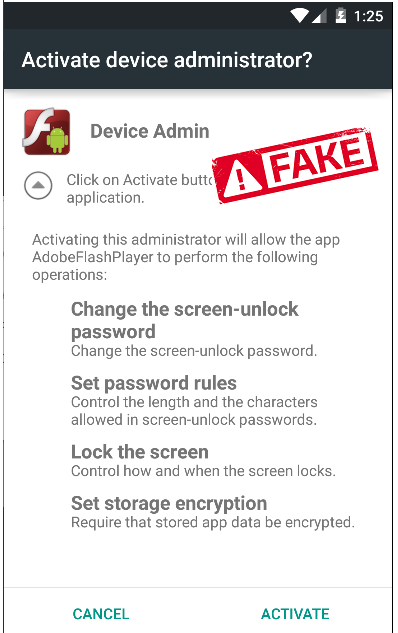
- An update screen for Adobe Flash Player appears. It looks realistic enough to deceive most users. It claims that it’s mandatory to protect against cyberattacks.
- If clicked, another screen appears warning that the installation is using too much battery power and needs to be switched over to a new “Saving Battery Mode” function because the “regular” battery indicator is broken. This dialogue will not disappear unless this “new mode” is enabled.
- Assuming the user clicks it (which is not recommended), the Android Accessibility Menu is opened. Included in the list are the actual services available and the new “Saving Battery” option.
- It then requests permission to do a lot of things: Monitor activities, retrieve content, and turn on the “Explore by Touch” function.
- It downloads malware at which time the fake flash player is enabled, but stays hidden.
- The malware contacts the command and control (C&C) center and sends information retrieved from the device.
- Additional malware is sent back from the C&C center and the screen displays a fake lock screen while it’s being installed. This fake screen cannot be closed.
- Malware is installed and the fake lock screen disappears.
- Hackers begin spying on the user.
 Should you discover this happened to you, you can take a couple of actions to attempt to eradicate it. First, uninstall the fake Adobe Flash Player app that appears on the device somewhere.
Should you discover this happened to you, you can take a couple of actions to attempt to eradicate it. First, uninstall the fake Adobe Flash Player app that appears on the device somewhere.
Run your anti-malware/anti-virus application to attempt to remove it. However, don’t count on those two steps to completely fix the issue.
You should completely reset your device to factory and reinstall from a previously safe backup. Remember at the beginning when it was recommended to do regular backups? This is when one of those will come in very handy.
 If you ever see a dialogue appear that says an update is available, make sure the update is coming from the official app store for your device. In this case, that’s the Google Play Store. Also, never give permissions to apps that they don’t need. It is a very unusual case that an app needs administrator rights, for example. Consider the app before letting it access your microphone, camera, or address book. If you are using a photo-editing app, for instance, it doesn’t need to know who your contacts may be.
If you ever see a dialogue appear that says an update is available, make sure the update is coming from the official app store for your device. In this case, that’s the Google Play Store. Also, never give permissions to apps that they don’t need. It is a very unusual case that an app needs administrator rights, for example. Consider the app before letting it access your microphone, camera, or address book. If you are using a photo-editing app, for instance, it doesn’t need to know who your contacts may be.
This Trojan is distributed via social media and compromised websites. Often, the websites in question are those that are more “adult focused,” which is a familiar delivery method for malware. Be very careful about sites visited and any links clicked in social media. If you are not completely sure they are safe, don’t go to them or follow them.