When the company PhishMe analyzed data from its anti-phishing products, it found some shockingly disappointing information. While it was no surprise that phishing is the top cybersecurity defense challenge to organizations, what was somewhat alarming was that 91% of the cyberattacks that occurred in 2015 and the data breaches into the organizations that followed them were the result of someone in that organization falling victim to a spear phishing attack.
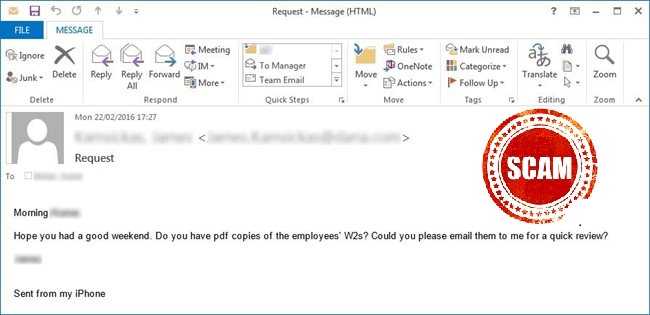 Spear phishing involves targeted attacks specifically designed to steal very sensitive information such as what is included on W-2 forms or to steal money via fraudulent wire transfers. Often, the scammer pretends to be an executive or manager in an email message requesting one of these items, or potentially other sensitive information.
Spear phishing involves targeted attacks specifically designed to steal very sensitive information such as what is included on W-2 forms or to steal money via fraudulent wire transfers. Often, the scammer pretends to be an executive or manager in an email message requesting one of these items, or potentially other sensitive information.
This report found that spear phishing like this rose 55% from the prior year. Those in the healthcare industry are particularly at risk. In the analysis, 31% of them fell for phishing in a simulated test, even after receiving training as to what to look for when it comes to phishing.
And what do you look for? There are several clues:
 1) Watch for typos, grammatical errors, formatting issues, and improper use of the language in which the email is written. While phishing messages are getting more difficult to detect these days, these little clues still often appear.
1) Watch for typos, grammatical errors, formatting issues, and improper use of the language in which the email is written. While phishing messages are getting more difficult to detect these days, these little clues still often appear.
2) If links or attachments are included in any email message, text, or other electronic communication, use extreme caution, particularly if you are not expecting them. Often included in such items is malware that can assist a scammer with spear phishing into an organization.
3) Hover over any links with the mouse pointer before clicking them to ensure they really go where you expect them to take you. If you are using a mobile device, many of them have a feature where you can hold your finger on the link for several seconds to see it in its entirety. It also may be possible to have it spoken back to you. If you see or hear a lot of extra hyphens or underscores, that link may be hiding something nefarious. This happened with a recent scam using fake Facebook links.
4) If ever in doubt of the legitimacy of anything included in an email, you can usually do a quick search online to see if it could be a scam. If it is, there will be information about it.
5) Use multifactor authentication (MFA) when it is offered to log into accounts such as for making financial inquires or transactions. This could involve entering a one-time text code, a one-time randomly generated code from a fob of some type, or answering additional security questions before access is granted. This will prevent someone from accessing your accounts even if the login and password combination is accessed.
6) Use caution about what you post on public Internet sites, such as for networking or even on social media pages. Spear phishermen often peruse those sites looking for targets working in particular departments. If you have a profile on a site such as LinkedIn, consider using a description of your responsibilities in general terms as opposed to your title; especially if you work in human resources, accounting, or finance. Make sure to check privacy settings for these sites to keep the information on them accessible to the fewest viewers possible.
 And always remember that email is not a secure form of communication in most cases. Consider anything you email as in public domain. Never send sensitive or confidential data through email unless you are certain it is encrypted and secured. And finally, know that every single employee of a company is a potential target. A hacker only needs one person to fall for the scam to potentially access the entire company network. Security is everyone's job.
And always remember that email is not a secure form of communication in most cases. Consider anything you email as in public domain. Never send sensitive or confidential data through email unless you are certain it is encrypted and secured. And finally, know that every single employee of a company is a potential target. A hacker only needs one person to fall for the scam to potentially access the entire company network. Security is everyone's job.